In This Article
Build technical trust with compliance-focused, practitioner-driven content and AI-assisted workflows for cybersecurity startups.
Updated:
Trusted by 1,000+ teams
Startups use Averi to build
content engines that rank.
Content marketing is critical for cybersecurity startups because buyers demand trust, expertise, and actionable insights. Traditional advertising often falls short since 81% of buyer interactions occur on non-sponsored content, and buyers typically review 13+ pieces of content before engaging with a vendor. With sales cycles lasting 9–18 months and involving multiple stakeholders, startups must create targeted, high-quality content addressing specific concerns like compliance, risk, and ROI.
Key takeaways:
Trust over fear: Avoid scare tactics; focus on expertise and measurable results.
Stakeholder-specific focus: Tailor content to CISOs, engineers, CFOs, and procurement teams.
Compliance-driven content: Address frameworks like SOC 2, HIPAA, and CMMC.
Leverage AI: AI tools can help small teams produce consistent, accurate content while reducing costs.
Actionable formats: Use how-to guides, case studies, and integration walkthroughs to engage technically savvy audiences.
Optimize | Meg Scarborough on Content Strategy, Cybersecurity Marketing, and AI's Impact on SEO
Mapping Cybersecurity Buyers and Content Opportunities
To earn trust and grow your audience in the cybersecurity space, you need content that speaks directly to the unique needs of its buyers.
Identifying Cybersecurity Buyer Personas
Cybersecurity buyers represent one of the most intricate decision-making groups in B2B. Understanding their priorities is key to creating content that resonates.
Broadly, these buyers fall into three categories. Technical buyers, such as CISOs and Security Architects, focus on topics like risk quantification, threat modeling, and compliance frameworks like NIST CSF 2.0. Business stakeholders, including CTOs and IT Directors, care more about integration, deployment speed, and operational efficiency. Meanwhile, SMB owners, who often lack dedicated security teams, look for easy-to-use dashboards, automated compliance tools, and phishing simulations they can manage independently [6].
Persona | Primary Concern | Content That Works |
|---|---|---|
CISO | Risk ROI, cyber insurance, SEC disclosure | FAIR model breakdowns, peer benchmarks |
CTO | API flexibility, cloud-native integration | Technical specs, architecture deep-dives |
IT Director | Deployment speed, patch automation | ROI calculators, sub‑1‑hour setup guides |
SMB Owner | Simplified management, compliance | Unified dashboards and checklists |
Another often-overlooked persona is the "Overwhelmed MSP" - managed service providers dealing with alert fatigue and juggling white-labeled reporting for multiple clients [6]. If your company sells through channel partners, this persona demands its own tailored content.
"Cybersecurity buyers are among the most skeptical, technically literate audiences in B2B." - Arete Intelligence Lab [1]
By aligning your content topics with the specific challenges of each persona, you can better address their concerns and build trust.
Turning Security Problems into Content Topics
The best cybersecurity content starts by addressing a specific, relatable problem - not by highlighting product features. For example, instead of focusing on "our AI-powered threat detection platform", consider topics like "how to prioritize 4,000 security alerts in your queue" [7].
Compliance requirements are a strong entry point. Content focused on SOC 2, HIPAA, or CMMC can resonate during high-pressure moments like audit season, new contract negotiations, or board reviews. Once you've addressed compliance concerns, you can shift to broader security challenges [9].
Organizing content by the buyer's immediate task is another effective strategy. For instance, a CISO preparing for a board presentation has different needs than a Security Architect evaluating tools. By focusing on the job the buyer is trying to accomplish, rather than your product’s features, your topics stay relevant and actionable [5].
This approach also naturally feeds into competitive and gap analysis, helping you refine your content strategy.
Running a Simple Competitive and Gap Analysis
With over 3,500 cybersecurity vendors worldwide [7], standing out is essential. A quick competitor audit can help you pinpoint opportunities.
Start by reviewing the blogs of your top 3–5 competitors. Pay attention to two things: the topics they cover consistently and the gaps they leave unaddressed. Many vendors rely heavily on fear-based messaging, which creates an opening for those willing to take a different approach. Consider producing in-depth technical guides, honest product comparisons, or detailed integration walkthroughs - content that larger vendors often overlook [7].
"If fear is your primary marketing lever, you are competing on the same axis as every other vendor, and you are doing it in a way that your best prospects have learned to ignore." - UpliftGTM [7]
Another area to explore is content debt - outdated posts that still rank but no longer reflect current threats. Refreshing these with updated, forward-looking insights (e.g., a 2026-ready version) can help you capture search traffic without starting from scratch [7]. Tools like Averi make this process easier by monitoring competitors’ content and alerting you to opportunities for counter-angles before the moment passes.
Building a Scalable Content Strategy for Cybersecurity Startups
AI-Assisted vs. Traditional Content Workflows for Cybersecurity Startups
Defining a Focused, High-Impact Content Plan
Once you’ve identified your audience and pinpointed content gaps, it’s time to craft a targeted plan. For smaller teams, this means concentrating on a few content types that deliver the most impact.
Today, generic content doesn’t cut it. What performs well are industry-specific and compliance-focused pieces - think SOC 2 readiness guides for SaaS companies, CMMC checklists tailored for defense contractors, or HIPAA compliance walkthroughs for healthcare IT teams. Long-form technical articles, ranging from 1,800 to 3,400 words, are especially effective, generating 4.1 times more qualified inbound leads than shorter posts when targeting B2B security audiences [1].
Timing is everything. Align your content releases with key product milestones. Launching a new integration? Publish a technical walkthrough that same week. Rolling out a compliance feature? Pair it with a guide tailored to the specific regulatory audience it serves. This keeps your content fresh and ensures marketing doesn’t become a bottleneck. Once your plan is in place, AI tools can help maintain a steady flow of content production.
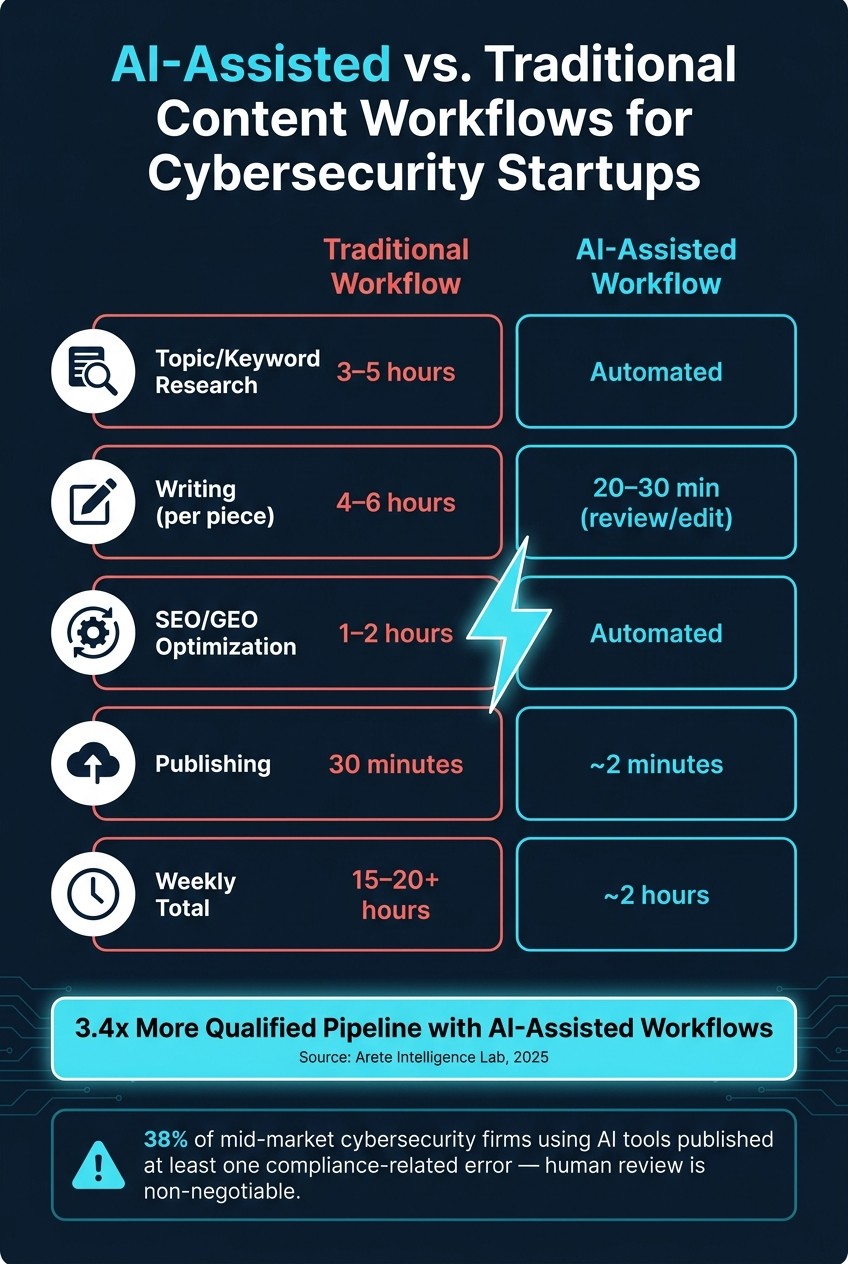
Setting Up AI-Driven Content Workflows
AI tools can be a game-changer, streamlining your content creation process and saving valuable time. Tasks that might take 15–20 hours manually can be condensed into just 2 hours with AI assistance. Here’s a breakdown of where the time savings happen:
Activity | Traditional Workflow | AI-Assisted Workflow |
|---|---|---|
Topic/Keyword Research | 3–5 hours | Automated |
Writing (per piece) | 4–6 hours | 20–30 min (review/edit) |
SEO/GEO Optimization | 1–2 hours | Automated |
Publishing | 30 minutes | ~2 minutes |
Weekly Total | 15–20+ hours | ~2 hours |
Platforms like Averi can manage the entire process - from analyzing your website to understand your brand voice, to generating a content queue based on keyword gaps and competitor analysis, to drafting SEO-optimized content and publishing directly to platforms like Webflow, Framer, or WordPress. Every piece of content feeds back into the system, improving its ability to match your tone and positioning over time.
One efficient workflow to consider is the "Research-Thursday" cadence. Here’s how it works: dedicate 30 minutes to record an engineer or security researcher demonstrating a technique or explaining a threat scenario. That recording becomes the foundation for multiple content pieces - a technical blog post, a LinkedIn carousel, and a set of FAQ entries - all drafted by AI. This approach minimizes the burden on your technical team while keeping the content grounded in real expertise [3].
Why Human Review Still Matters
Even with the efficiency of AI, human oversight is non-negotiable. While AI can draft content quickly, expert review ensures accuracy, particularly for nuanced applications like how HIPAA regulations apply to a specific dental practice or how CMMC Level 2 requirements align with a contractor’s environment. In fact, 38% of mid-market cybersecurity firms using AI tools in 2025 published at least one compliance-related error [1].
"In cybersecurity, a single AI-generated compliance error can cost more than an entire quarter's content budget to remediate." - Arete Intelligence Lab [1]
To mitigate these risks, a two-stage review process is essential. First, a qualified practitioner verifies the technical details. Then, a legal or risk expert conducts a compliance check. Beyond avoiding costly mistakes, human attribution also boosts content credibility. Publishing content under the name of a verified expert - such as an engineer or researcher - makes it 3.2 times more likely to be cited by AI recommendation systems like ChatGPT and Perplexity [9]. In an era where AI-driven discovery plays a major role in buyer decisions, this kind of attribution isn’t just about credibility - it’s a crucial strategy for distribution.
Creating High-Value Content for Cybersecurity Audiences
Crafting content for cybersecurity professionals demands precision, depth, and actionable insights. These buyers are not swayed by marketing fluff. They are technically savvy, highly skeptical, and have likely encountered every "game-changing" AI claim out there. What resonates with them is hard evidence - specific, well-documented insights rooted in practical scenarios. Research shows that B2B buyers review 5–7 pieces of content before making a purchase decision [8]. This highlights the importance of offering a diverse and comprehensive content library that supports every stage of their evaluation process.
Writing Practical How-To Guides and Playbooks
Cybersecurity professionals value guides that deliver actionable instructions. For instance, a guide titled "How to Detect Source-Code Exfiltration to GitHub Over HTTPS" is far more impactful than a generic overview like "Introduction to Data Loss Prevention." The more specific the scenario, the more useful and credible the content becomes in the eyes of practitioners who will rigorously test the recommendations.
"Cybersecurity buyers are allergic to puff pieces. They want proof - tactics, packet captures, and mitigation guides that stand up to a penetration test." - Abhimanyu Singh, Engineering Manager [3]
The structure of these guides is crucial. A robust playbook should include:
A detailed threat scenario
Detection logic
MITRE ATT&CK mapping, where relevant
Step-by-step mitigation instructions
For US audiences, connecting these guides to compliance frameworks like SOC 2, CMMC, or HIPAA adds another layer of relevance, as these frameworks directly tie to business risks. Including FAQPage schema markup can also improve visibility in AI-powered search tools like Perplexity [3]. This hands-on approach not only builds trust but also lays the groundwork for more advanced content, such as thought leadership.
Producing Thought Leadership and Research Content
In addition to practical guides, original research and expert analysis can significantly boost a brand's authority. Thought leadership stands out when it's backed by unique data or direct technical expertise, not just rehashed industry reports. Formats like original threat research, detailed breakdowns of attack techniques, and compliance strategies addressing new regulations consistently resonate with cybersecurity audiences [7].
A consistent research cadence allows you to create content tailored for both technical and executive audiences. For example, a technical metric like "60% reduction in MTTR" can be translated into business terms, such as "$400,000 saved per incident", to engage decision-makers [11].
Attributing such content to a verified expert, rather than a generic "Company Blog" byline, aligns with Google's E-E-A-T (Experience, Expertise, Authoritativeness, Trustworthiness) guidelines. This makes your content 3.2 times more likely to be cited by AI platforms like ChatGPT [9].
Using Case Studies and Integration Guides to Build Trust
Case studies and integration guides are essential for building credibility with cybersecurity buyers. With 78% of B2B buyers consulting case studies during their evaluation process [8], these assets carry significant weight. However, vague testimonials won't cut it. Effective case studies must include specifics like the industry, company size, technical environment, and measurable outcomes.
"A case study showing how a similar company reduced incident response time by 60% or cut false positives by 80% is more persuasive than any product page." - Otrenix [11]
If naming a client isn't possible due to confidentiality, anonymized case studies can still be impactful. For example, describing "a 200-person healthcare SaaS company managing PHI under HIPAA" provides enough context to make the story relatable and credible [2].
Integration guides demand the same level of detail. Buyers want to see exactly how your product works with their existing tools, such as SIEM, SOAR, or ticketing systems - not just a generic diagram. Treat these guides as an integral part of your product offering. Pairing them with a free trial or sandbox environment allows practitioners to test your solution hands-on, giving them the confidence to advocate for it within their organization [11].
Scaling and Measuring Your Content Marketing Engine
Scaling your content production ensures both consistent output and the reinforcement of trust - a cornerstone in cybersecurity marketing.
Building a Repeatable Weekly Content Workflow
Publishing once a month won’t cut it for startups trying to stand out in a competitive space. Consistency is the game-changer, but for lean teams, the challenge lies in creating a system that doesn’t crumble during a busy product sprint.
One effective approach is the "Research Thursday" workflow. This involves recording a single expert session and repurposing it into several assets - like a technical blog post, a LinkedIn carousel, and an FAQ page - without starting from scratch [3].
"The cure is not simply 'hire more people.' First, design a system - clear ownership, modular work slices, and lightweight automation - so that added humans amplify speed rather than clogging it." - Abhimanyu Singh, Engineering Manager & AI Builder [3]
Teams that thrive treat content like software, automating tasks such as version control, previews, and SEO checks [3]. AI takes care of initial drafts, topic clustering, and metadata, while subject-matter experts refine the content for accuracy and proprietary insights before publishing [1]. Cybersecurity firms using such AI-assisted workflows report 3.4x more qualified pipeline compared to those relying solely on manual production [1].
Tracking Performance and Refining Your Content
With a streamlined workflow in place, the next step is monitoring metrics that truly impact your pipeline. Pageviews alone don’t reveal much. Instead, focus on whether your content - like a technical guide - helps move a security engineer closer to requesting a demo. Key metrics to track include:
Metric Category | Key Performance Indicator | Why It Matters |
|---|---|---|
Pipeline | Content-Sourced Pipeline Influence | Links specific content to closed-won deals in your CRM [4] |
Conversion | Download-to-Demo Conversion Rate | Indicates if educational content is driving genuine sales intent [4] |
Visibility | AI Citation Frequency | Tracks how often your brand appears in ChatGPT or Perplexity answers [9] |
Authority | Vertical-Specific Keyword Rankings | Demonstrates expertise in niche areas like SOC 2 or CMMC compliance [9] |
Operations | Content Cycle Time | Highlights bottlenecks by measuring time from concept to publish [3] |
In 2026, Rachel Okafor, VP of Marketing at a $38M managed security services firm, revamped her AI-driven content strategy to focus on distribution and personalization. Within six months, qualified leads jumped from 18 to 41 per quarter, while overall content spending dropped by 19% [1].
"AI content velocity is a compounding asset: each published piece increases topical authority, which lowers CAC on every piece that follows." - Arete Intelligence Lab [1]
Regular updates to compliance guides and threat briefings are essential. Both search engines and AI recommendation systems favor fresh content, and in cybersecurity, outdated information can erode trust [9].
Comparing Automation Options for Lean Teams
To maximize your workflow’s potential, choosing the right automation tools is crucial. The needs of a solo founder differ greatly from those of a 10-person marketing team at a Series A company. Below is a comparison of three primary automation tool categories:
Feature | AI-Driven Workspaces (e.g., Averi) | Point Tools (e.g., Jasper, ChatGPT + SEO tools) | Talent Marketplaces (e.g., Upwork, MarketerHire) |
|---|---|---|---|
Efficiency | High; integrates strategy, drafting, and publishing [10] | Moderate; fragmented tools require more oversight | Low; high management overhead for small teams [3] |
Consistency | High; maintains brand voice across drafts [10] | Low; manual prompting needed for each asset | Variable; depends on freelancer quality |
Scalability | High; enables 10x output without growing headcount [10] | Moderate; limited by operator capacity | Moderate; scales with budget rather than systems |
Best Fit | Startups needing an end-to-end solution | Teams scaling specific formats like social posts or ads | High-stakes, one-off projects like whitepapers |
Costs vary widely. Seed-stage startups typically spend $200–$500 per month on tools, while growth-stage teams with structured AI content programs allocate $2,000–$8,000 monthly [10]. However, one often-overlooked expense is compliance errors. 38% of mid-market cybersecurity firms using AI tools have published content with compliance-related inaccuracies [1], and fixing a single error can cost around $14,200 [1]. This makes human subject-matter expert review an essential step, no matter which tool you choose.
Conclusion and Key Takeaways
In cybersecurity, trust isn’t earned with scare tactics - it’s built through content rooted in technical expertise. Today’s buyers, particularly CISOs and security engineers, have grown weary of fear-based messaging. They’re looking for practitioner-driven insights, original research, and straightforward case studies that genuinely help them tackle their challenges. The companies making headway are those delivering content that informs and empowers, not intimidates.
The most effective approach combines AI and human expertise. AI takes care of tasks like research, initial drafts, SEO frameworks, and performance tracking, while skilled practitioners ensure the content is technically accurate and offers unique insights. This collaboration is essential, as a two-stage review process - covering technical accuracy and compliance - has been shown to reduce AI-related compliance errors by 91% [1]. Simply put, expert oversight is non-negotiable.
"Technical credibility is not optional in cybersecurity content: it is the only currency that opens doors at the CISO level." - Arete Intelligence Lab [1]
AI-powered content workflows also deliver measurable results, such as increasing qualified leads and lowering acquisition costs [1]. Tools like Averi streamline the entire content process - from strategy and drafting to publishing and analytics - allowing smaller teams to maintain steady output without expanding their staff. These efficiencies highlight why aligning content with buyer priorities is so impactful.
To resonate with your audience, focus on their goals rather than your product’s features. Topics like "how to detect lateral movement" or "SOC 2 readiness checklist" directly address the tasks security teams are managing. This practical, buyer-focused strategy not only builds trust but also drives meaningful outcomes.
FAQs
Which cybersecurity buyer persona should I target first?
When targeting cybersecurity decision-makers such as CIOs, CISOs, and other security leaders, it's essential to understand their mindset. These individuals are naturally cautious and prioritize trust, credibility, and strong validation before making decisions. As a result, they represent the most critical audience to engage with during the early stages of your content marketing strategy. Tailoring your approach to address their concerns and establish confidence can make all the difference in gaining their attention and trust.
How can I use AI to scale content without risking compliance errors?
To expand content production using AI without running into compliance issues, combine AI-powered workflows with human supervision. Use AI to handle tasks such as drafting and editing, but always have a human review the output to ensure it adheres to industry regulations and aligns with brand guidelines. Set up clear policies, implement multiple review stages, and utilize AI tools to flag potential risks, such as sensitive information or inaccurate claims. Regularly update and enhance your processes to keep pace with changing regulations while maintaining high-quality standards.
What metrics show content is driving pipeline, not just traffic?
When evaluating whether your content is contributing to pipeline growth, focus on metrics that truly matter. Key indicators include qualified lead volume, conversion rates, and engagement metrics directly tied to sales outcomes, such as pipeline expansion. Instead of getting distracted by surface-level data like page views or general traffic, prioritize insights that highlight the generation of high-quality leads and impactful interactions.
Related Blog Posts

Zach Chmael
CMO, Averi
"We built Averi around the exact workflow we've used to scale our web traffic over 6000% in the last 6 months."
Your content should be working harder.
Averi's content engine builds Google entity authority, drives AI citations, and scales your visibility so you can get more customers.




